Blog
iCostamp: Understanding its Purpose, Structure, and Potential

the term iCostamp has emerged within specialized circles discussing digital authentication and secure document verification. At its core, refers to a proposed framework combining cryptographic hashing, blockchain anchoring, and dynamic metadata layering to produce a tamper-evident “stamp” that can be affixed to digital files, documents, and media. While not yet widely adopted, early whitepapers and proofs-of-concept suggest that could play a significant role in shaping how we trust, share, and archive digital content in the coming years. This article aims to present a comprehensive overview of: its origin, technical architecture, intended use cases, current limitations, and potential future implications.
Origins of iCostamp
The concept of iCostamp was first floated in a technical memorandum circulated among a group of independent cybersecurity researchers in late 2023. They observed a growing need for a universal mechanism to prove document provenance and integrity — especially as deepfakes, forged documents, and illicit content manipulation became more prevalent. According to the initial authors, was inspired by traditional notary stamps and wax seals, transposed into the digital age. Instead of physically sealing a letter, provides an immutable digital seal, proving that the content has not been altered since the seal was applied. Over time, the design evolved through community collaboration, integrating feedback from cryptographers, archivists, and legal-tech specialists.
What Does the Name Mean?
The term “iCostamp” blends several conceptual components. The “iCo” prefix loosely references “integrity and confirmation,” while “stamp” evokes the idea of a seal or approval mark. Thus, iCostamp effectively designates a digital proof mark asserting the integrity and authenticity of a document. From the outset, the creators emphasized that should remain technology-agnostic: able to operate atop various file systems, cloud services, or content-delivery networks. Its goal is not to enforce a single standard, but to define a minimal set of rules and structures allowing interoperability and verification across platforms.
Technical Architecture — Core Components (Part 1)
At the heart of iCostamp lies a combination of cryptographic hashing and metadata encapsulation. When a user “applies” an iCostamp to a document, the system computes a cryptographic hash (e.g., SHA-3 512 or BLAKE3) over the entire file, ensuring that any subsequent change — even a single byte — results in a different hash. This hash value becomes the “core fingerprint.” Simultaneously, a metadata package is generated: including timestamp, author identifier (public key), document name, version number, and optionally a user-defined description or tags. The metadata package and fingerprint are then bundled together in a signed container, signed by the user’s private key associated with their public identifier. That signature certifies who applied the iCostamp.
Technical Architecture — Anchoring and Verification (Part 2)
Once the signed container is ready, iCostamp offers two optional — but strongly recommended — anchoring methods. First, the container can be submitted to a public or private blockchain (or distributed ledger) to embed the hash as a transaction data field, creating an immutable timestamping anchor. This ensures that even if the original file and metadata container are lost, the proof of existence remains verifiable on the ledger. Second, for scenarios where blockchain anchoring is impractical, supports a decentralized peer-to-peer registry: a network of validator nodes that collectively maintain a ledger of issued stamps, including hash values and signatures. Anyone with access to the original file and the signed container can re-compute the hash and verify the signature, thereby confirming whether the file remains unaltered and whether the belongs to a recognized issuer.
Primary Use Cases of iCostamp (Part 1)
One of the most touted applications for is in academic publishing and research archiving. Researchers frequently deal with manuscripts, datasets, and supplementary materials whose integrity is crucial over long periods. By stamping each version of a paper or dataset with iCostamp, authors can later prove which version was original — helping to prevent disputes over priority, plagiarism, or unauthorized changes. Librarians and institutions can also use to manage archival records, ensuring that digital archives remain intact even after migration across storage systems.
Primary Use Cases of iCostamp (Part 2)
Another promising area is legal documentation and digital contracts. As businesses increasingly rely on electronically signed contracts, invoices, and compliance documents, the risk of tampering or unauthorized edits grows. iCostamp can serve as an independent verification layer: after a contract is signed (perhaps via an e-signature), applying an locks the final signed version, providing a cryptographic assurance of integrity. For regulators, auditors, or courts, this can help validate that a contract has not been altered post-execution. The metadata within the stamp (timestamp, author identity, version) further strengthens the evidentiary value.
Security Features and Integrity Guarantees
The design of iCostamp offers multiple layers of security. The cryptographic hash ensures file immutability; the digital signature ties the stamp to a specific identity; and the blockchain anchor (or decentralized registry) adds a tamper-resistant timestamping layer. Combined, these measures create a strong non-repudiation guarantee: a malicious adversary would need to compromise the private key, alter the file, and also rewrite the blockchain transaction — a task that is practically infeasible under standard security assumptions. Additionally, because iCostamp is file-agnostic, it works equally well for text documents, images, audio, video, or compressed archives, offering a unified verification approach across media types.
Limitations and Challenges (Part 1)
Despite its promise, iCostamp faces significant challenges before widespread adoption. One major obstacle is usability: the average user may find the process of computing hashes, managing keys, and anchoring stamps on a blockchain too technical. Without user-friendly tools or seamless integration into popular applications (like word processors or cloud storage services), iCostamp risks remaining a niche solution for experts. In response, early proponents have discussed developing browser extensions or plugins to automate stamping and verification — but as of mid-2025, none have matured into widely used software.
Limitations and Challenges (Part 2)
Another significant concern is scalability and cost, especially with blockchain anchoring. Embedding a hash in a public blockchain transaction incurs fees and depends on network conditions and transaction throughput. For individuals or small organizations, repeated stamping of multiple files may become cost-prohibitive. The decentralized registry alternative reduces costs but introduces issues around trust and decentralization: if a registry’s validator nodes are few or centralized, the integrity assurance could suffer. Finally, long-term preservation raises questions: will metadata containers and signed stamps remain readable in decades to come? Will cryptographic algorithms (hash and signature schemes) stay secure over time, or become vulnerable to advances in computing — including quantum computing?
Current Adoption and Industry Response
As of late 2025, adoption of iCostamp remains limited, largely confined to academic proof-of-concepts, niche legal-tech startups, and a handful of digital-archiving nonprofits. Some universities have piloted its use for dataset publication; a few open-source legal-document platforms offer experimental integration. However, mainstream cloud providers and large document-management services have not endorsed or built support for. Feedback from industry stakeholders tends to emphasize the gap between cryptographic promise and user convenience: many note that until iCostamp becomes invisible to end-users — integrated seamlessly behind “save” buttons or cloud-sync workflows — its impact will remain marginal.
Future Outlook for iCostamp
Looking ahead, the future of depends heavily on bridging the usability gap and building broader consensus. If developers create intuitive tools — for instance, plugins that automatically stamp every saved file, or cloud-storage providers that offer “stamp-and-archive” features — iCostamp could gain traction. Additionally, rising regulatory interest in digital integrity, especially for financial, legal, or governmental records, may incentivize adoption. As laws and standards around digital records evolve, entities may begin to require cryptographic proofs of integrity — an environment in which iCostamp-like frameworks could become default practice. There is also potential for to evolve: future versions might support version chaining (creating a chain of stamps reflecting document history), multi-party stamping (for collaborative edits), or integration with decentralized identity standards, strengthening provenance and trust.
Conclusion
The concept of iCostamp offers a compelling vision for how we might anchor trust, authenticity, and integrity in the digital age. By applying cryptographic hashing, metadata encapsulation, digital signatures, and optional decentralized anchoring, transforms ephemeral digital documents into verifiable, tamper-evident artifacts. Its proposed benefits — from safeguarding academic research to securing legal contracts — are real and relevant. Yet, as with many promising technologies, its success hinges on bridging the gap between technical robustness and user usability. Until user-friendly tools, widespread integration, and perhaps even regulatory demand materialize, remains an intriguing but under-utilized solution. However, if the right ecosystem begins to form, iCostamp could one day become a foundational element of digital trust infrastructure.
-
 Celebrity1 year ago
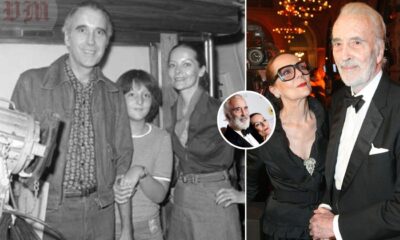
Celebrity1 year agoChristina Erika Carandini Lee: A Life of Grace, Heritage, and Privacy
-

 Celebrity1 year ago
Celebrity1 year agoTrey Kulley Majors: The Untold Story of Lee Majors’ Son
-

 Celebrity12 months ago
Celebrity12 months agoNick Schmit? The Man Behind Jonathan Capehart Success
-

 Celebrity1 year ago
Celebrity1 year agoJamie White-Welling: Bio, Career, and Hollywood Connection Life with Tom Welling
















