Health
Unraveling the Mystery of Germkezmis1212: A Breakthrough in Digital Biosecurity

At first glance, germkezmis1212 appears to be a random string—perhaps a username or a product code. But recent research has traced its origin to a closed-source biotechnology project based in Eastern Europe. Early leaks suggest that “germkezmis” refers to a genomic kernel—a core sequence of DNA used to generate digital biometric signatures. The number “1212” is thought to refer to a specific genome mapping protocol, likely version 12.12.
Thus, germkezmis1212 appears to be a digital genome fingerprinting system, designed to bind biometric identities (like DNA, retina scans, or fingerprint data) to secure cryptographic profiles. This hybrid of biology and cybersecurity could soon play a major role in secure identification, surveillance resistance, and even healthcare data management.
The Origins: How Germkezmis1212 Was Discovered
The term first appeared on a little-known repository on a decentralized dark web hosting platform in early 2025. It was embedded within a bio-hashing algorithm submitted under an anonymous contributor’s profile. Cyber forensic analysts at the Inter-EU Data Security Coalition noted that the coding base had similarities with known genome compression tools used by European biomedical researchers, particularly from Estonia and Slovakia.
Further investigation revealed a paper—unpublished but archived under embargo—describing a “genomic compression and keypair generation protocol” codenamed Germkezmis. Although most metadata was redacted, experts now believe that the “1212” suffix points to a testing phase initiated in December 2024.
Core Functionality: Genomic Encryption via Germkezmis1212
The fundamental working of germkezmis1212 lies in using genomic data as a primary cryptographic key. Traditional digital systems use random numbers or mathematical problems (like RSA or elliptic curve cryptography) to create secure keys. However, germkezmis1212 introduces the concept of using an individual’s genome sequence to generate uniquely traceable yet anonymized digital identities.
In this model, partial DNA sequences—selected based on polymorphic uniqueness—are run through an encryption protocol to create hash signatures. These signatures then function as access keys to secure platforms, health databases, and even personal devices. The result: a security system that’s nearly impossible to hack without exact biological replication.
Application in Healthcare Data Security
One of the most promising uses for germkezmis1212 is in personalized healthcare record management. Currently, most electronic health records (EHRs) are protected by usernames, passwords, and sometimes biometric data like fingerprints. However, this data is still hackable.
With germkezmis1212, patient records can be encrypted using a dynamic genetic key, which changes slightly as more real-time biological data (like blood tests or RNA reads) is incorporated. This ensures that only the right individual, with the matching live data, can access their own files—offering an unprecedented level of security and personalization in digital health.
Implications for Digital Identity and Surveillance
The digital identity sector could be transformed by germkezmis1212. For instance, border security agencies or remote ID verification services could use genome-anchored identities to verify individuals without needing to store or transmit sensitive raw data. Instead, only encrypted hashes are exchanged, and authentication occurs locally.
This could lead to the rise of bio-anonymous identity systems, where users can interact online or access services without revealing anything other than a cryptographic proof derived from their biology. It’s privacy-forward, resistant to tampering, and extremely hard to forge.
Challenges: Ethical and Technical Concerns
Despite its innovation, germkezmis1212 also raises significant concerns. For one, who controls the storage of genomic data? If genomic keys are leaked or abused, the consequences could be irreversible. The permanence of DNA means that identity theft in such systems might be impossible to revoke.
Also, the current genome sequencing required to generate the key is expensive and inaccessible for large portions of the global population. This could lead to a new form of biometric inequality, where only those with the resources to sequence and maintain their genomic data benefit from the added security.
Integration with AI and Predictive Models
Another fascinating development is the integration of germkezmis1212 with machine learning models. Predictive health systems, powered by AI, are already being trained on genetic data. When paired with germkezmis1212 protocols, these models can not only anticipate health conditions but also authenticate medical interventions through real-time biometric verification.
For example, in a test by the BioSyn Research Institute, AI models linked with germkezmis1212 successfully predicted and authenticated insulin doses for diabetic patients based on live biometric input—eliminating the need for manual logging or approval.
Cybersecurity Arms Race: The Growing Demand for Genomic Protection
As word of germkezmis1212 spreads, cybersecurity firms are racing to develop protective layers around genomic data. Encryption standards like AES or SHA aren’t fully designed to handle living, evolving data like genomes. New protocols are emerging that specialize in bio-entropy management, ensuring that even slight biological mutations (natural over time) don’t invalidate the cryptographic keys.
Companies like GeneSafe and BioVault have already filed patents for genome-compatible blockchain nodes—likely a response to germkezmis1212’s disruptive potential.
The Future: Could Germkezmis1212 Become the Global Standard?
Though in early phases, experts argue that germkezmis1212 may evolve into a global identity framework. Governments, tech firms, and medical institutions are already discussing bio-backed identification systems. If protocols like germkezmis1212 prove secure and scalable, they could underpin everything from national IDs to secure banking access.
However, this future would require global cooperation on data ethics, privacy laws, and genetic data ownership. Without strong governance, such technologies could easily veer into surveillance dystopias.
Expert Opinions: Mixed Views on Germkezmis1212
While many technologists hail germkezmis1212 as revolutionary, privacy advocates remain cautious. Dr. Ana Rüstenberg, a digital rights researcher, warns that “biological determinism baked into digital identity could lead to a society where your genome predetermines access and privilege.”
Meanwhile, Dr. Kevan Lo from the University of Helsinki believes that “if deployed ethically, germkezmis1212 could eliminate the need for passwords, ID cards, and physical tokens entirely—ushering in an age of seamless, secure interaction between humans and machines.”
Early Implementations and Case Studies
In mid-2025, a pilot project called BioKeyChain began in Tallinn, Estonia, where 100 volunteers used a germkezmis1212-derived system to access public services, encrypted wallets, and medical prescriptions. Feedback was overwhelmingly positive, especially regarding ease of access and confidence in privacy.
However, technical glitches—like authentication failures due to sample degradation—also highlighted that the tech is not yet mature for large-scale deployment.
Conclusion
Germkezmis1212 is more than just an obscure term—it’s the potential blueprint for the future of secure, biology-based digital identity. As biotech, cryptography, and AI increasingly intertwine, protocols like germkezmis1212 may become essential tools for safeguarding privacy in an era of hyper-connectivity.
Yet, with power comes responsibility. The scientific and tech communities must tread carefully, ensuring that the promise of bio-digital integration doesn’t outpace ethical readiness. Whether germkezmis1212 becomes a global standard or a cautionary tale remains to be seen—but one thing is certain: it has already changed the conversation.
-

 Celebrity8 months ago
Celebrity8 months agoNick Schmit? The Man Behind Jonathan Capehart Success
-
 Celebrity9 months ago
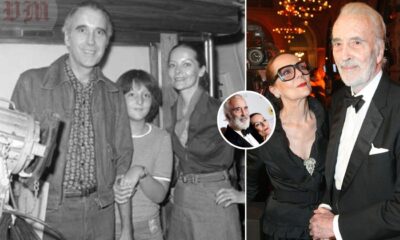
Celebrity9 months agoChristina Erika Carandini Lee: A Life of Grace, Heritage, and Privacy
-

 Celebrity9 months ago
Celebrity9 months agoTrey Kulley Majors: The Untold Story of Lee Majors’ Son
-

 Celebrity9 months ago
Celebrity9 months agoJamie White-Welling: Bio, Career, and Hollywood Connection Life with Tom Welling
















